OTSentry: Software-Defined Cybersecurity for CNI

Operational Technology networks were originally built for reliability and predictable operation, not for security. As these systems have become increasingly connected to corporate IT and the wider internet, they’ve become exposed to sophisticated attacks capable of issuing valid‑looking industrial commands and manipulating physical processes without triggering traditional alarms. Conventional IT defences don’t translate well here: PLCs can’t run endpoint agents, typical intrusion‑detection tools don’t understand industrial protocols, and external security appliances add latency and fragility to systems expected to run continuously.
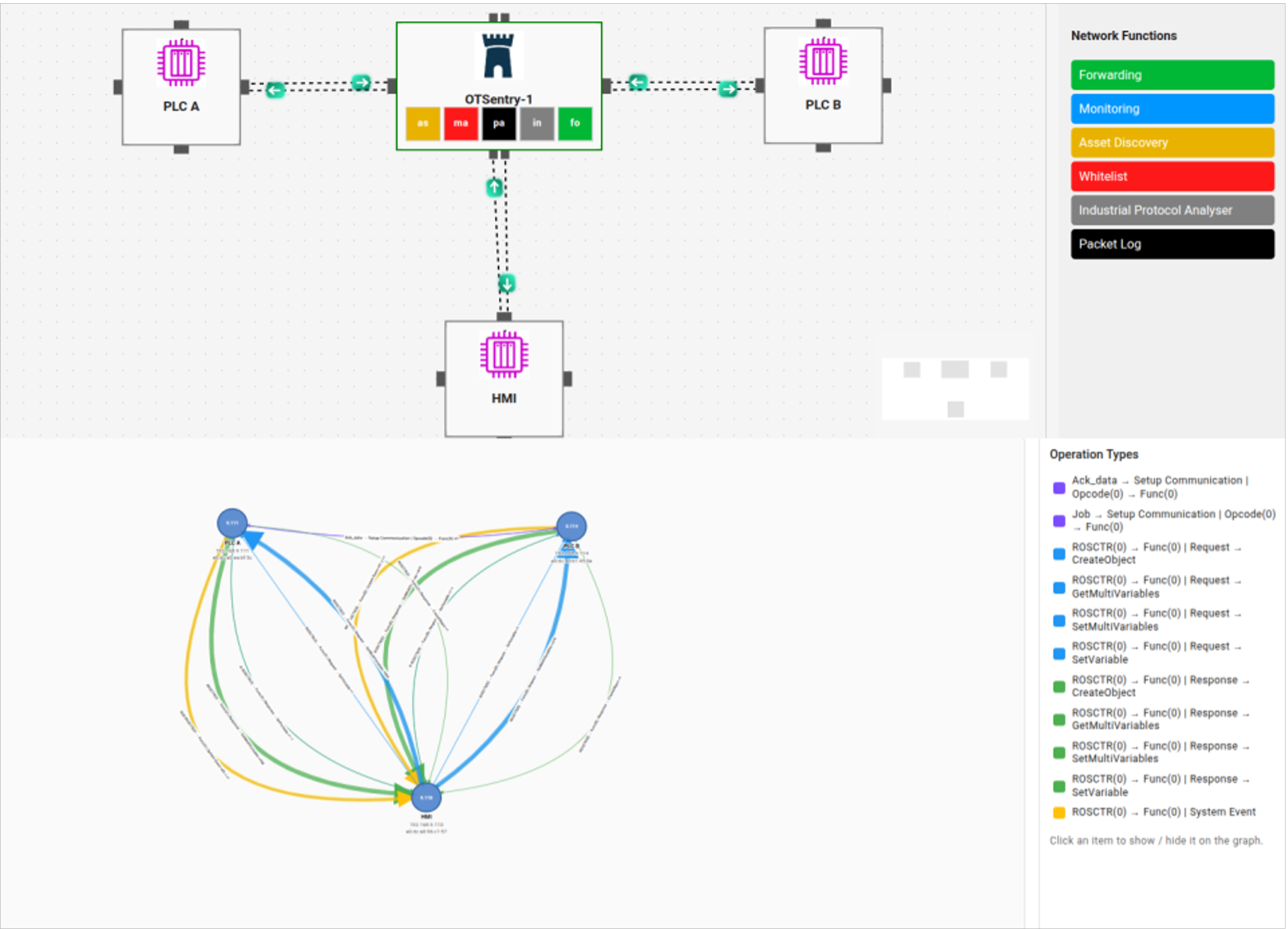
The research direction described reframes the problem: instead of bolting security onto OT networks, embed it directly into the network fabric. Using software‑defined, programmable switches, the network itself becomes a security platform capable of inspecting industrial traffic, understanding process context and enforcing policy in real time. OTSentry embodies this idea. It is a programmable industrial switch that forwards traffic like a normal field‑layer device while simultaneously analysing every frame, interpreting industrial protocols and monitoring process state. Its behaviour is defined entirely by modular security functions that can be added, removed or updated without downtime.
OTSentry is structured in three layers: a software data plane that handles all traffic; a library of composable, single‑purpose functions for tasks such as protocol parsing, access control and digital twinning; and a controller that manages these functions, performs higher‑level analysis and presents insights through a dashboard. By combining protocol visibility, process awareness and in‑line enforcement within the same device operators already deploy as a switch, this approach delivers adaptable, built‑in OT security without agents, extra appliances or rigid, hard‑coded defences.
Figure: OTSentry dashboard interface with network topology and security function chaining (top) and Industrial protocol flow detection (bottom).